3. AWS - Provision Infrastructure
Overview
The image below illustrates the multiple components deployed. These include the EKS, Worker Nodes, Postgres DB, EBS Volumes, and Load Balancer.

Steps
Clone the DIGIT-DevOps repository:
Navigate to the cloned repository and checkout the kubernetes-1.31 branch:
Check if the correct credentials are configured using the command below. Refer to the attached doc to setup AWS Account on the local machine.
Make sure that the above command reflects the set AWS credentials. Proceed once the details are confirmed. (If the credentials are not set follow Step 2 Setup AWS account )
Choose either method below to generate SSH key pairs
a. Use an online website (not recommended in a production setup. To be only used for demo setups): https://8gwifi.org/sshfunctions.jsp
b. Use openssl:
Add the public key to your GitHub account.
Open input.yaml file in vscode. Use the below code to open it in VS code:
code infra-as-code/terraform/sample-aws/input.yamlIf the command does not work, open the file in VS code manually. Once the file is open, fill in the inputs. (If you are not using vscode, open it in any editor of your choice).
Fill in the inputs as per the regex mentioned in the comments.
Go to infra-as-code/terraform/sample-aws and run init.go script to enrich different files based on input.yaml.
Terraform Execution: Infrastructure Resources Provisioning
Once we are complete declaring the resources, begin with deploying all resources.
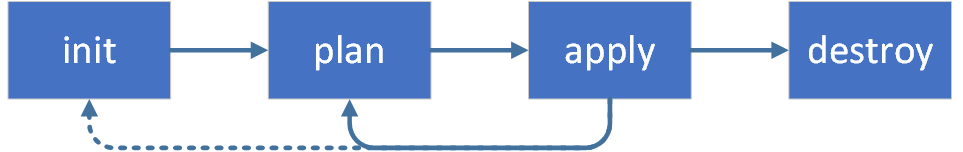
Run the terraform scripts to provision infra required to Deploy DIGIT on AWS.
CD (change directory) to the following directory and run the below commands to create the remote state.
Once the remote state is created, it is time to provision DIGIT infra. Run the below commands:
Important:
DB password is asked for in the application stage. Remember the password you have provided. It should be at least 8 characters long. Otherwise, RDS provisioning will fail.
The output of the apply command will be displayed on the console. Store this in a file somewhere. Values from this file will be used in the next step of deployment.
2. Use this link to get the kubeconfig from EKS for the cluster. The region code is the default region provided in the availability zones in variables.tf. For example - ap-south-1. EKS cluster name also should've been filled in variables.tf.
3. Verify that you can connect to the cluster by running the following command
At this point, your basic infra has been provisioned.
Note: Refer to the DIGIT deployment documentation to deploy DIGIT services.
Destroying Infra
To destroy the previously created infrastructure with Terraform, run the command below:
ELB is not deployed via Terraform. ELB was created at deployment time by the setup of Kubernetes Ingress. This has to be deleted manually by deleting the ingress service.
kubectl delete deployment nginx-ingress-controller -n <namespace>kubectl delete svc nginx-ingress-controller -n <namespace>Note: Namespace can be either egov or jenkins.
Delete S3 buckets manually from the AWS console and verify if ELB got deleted.
In case of if ELB is not deleted, you need to delete ELB from the AWS console.
Run
terraform destroy.
Sometimes all artefacts associated with a deployment cannot be deleted through Terraform. For example, RDS instances might have to be deleted manually. It is recommended to log in to the AWS management console and look through the infra to delete any remnants.
Last updated
Was this helpful?